Tag: EX200
How to Pass RHCSA EX200 Certification Exam in 1st Attem...
Aayushi Jun 18, 2024 1088
Unlock the secrets to acing the RHCSA EX200 Certification Exam on your first attempt with WebAsha Technologies! This comprehensive...
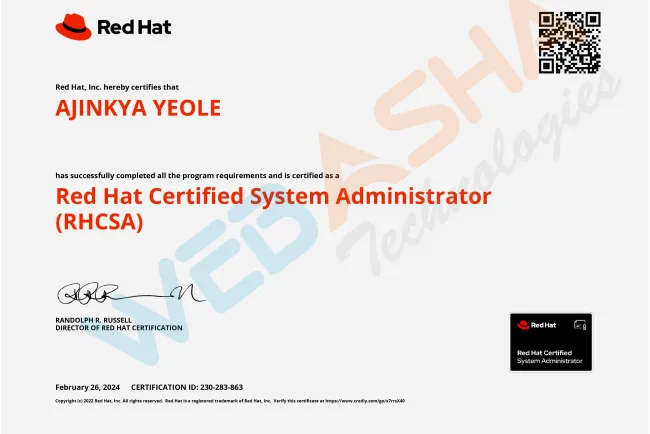
Ajinkya Yeole Has Successfully Completed Red Hat Certif...
Aayushi Mar 2, 2024 1212
Discover Ajinkya Yeole's success story in achieving the Red Hat Certified System Administrator (RHCSA) certification with the supp...
Popular Posts
-
Top 10 Ethical Hackers in the World [2025]
Aayushi Aug 19, 2024 18772
-
Which Is the Best Laptop For Cyber Security Course?
Anjali Aug 21, 2024 18728
-
[2025] Top 100+ VAPT Interview Questions and Answers
Aayushi Aug 28, 2023 17517
-
How to Install Red Hat Enterprise Linux (RHEL) 9 ? RHEL...
Aayushi May 18, 2022 17261
-
Get 50% Discount on Azure Certification Exam Voucher AZ...
Aayushi Oct 15, 2022 14383
Our Picks
-
Why is Certified Ethical Hacker (CEH v13 AI) So Popular...
Aayushi Jan 26, 2025 4567
-
Know Everything about RHCSA (Red Hat Certified System A...
Aayushi Sep 15, 2022 3024
-
How to Install Red Hat Enterprise Linux (RHEL) 9 ? RHEL...
Aayushi May 18, 2022 17261
-
Red Hat Remote Individual Certification Exams of RHCSA,...
Aayushi May 22, 2020 3432
-
What is kubernetes and Containers? Why is So Popular?
Aayushi May 15, 2020 2798
Categories
- Networking(6)
- Linux(57)
- PMP(2)
- Seo(6)
- Security(1056)
- Interview Q & A(255)
- Python Interview Q & A(13)
- Common Interview Q & A(17)
- Cloud Admin Interview Q & A(39)
- Linux System Admin Interview Q & A(14)
- Networking Interview Q & A(1)
- Penetration Testing Interview Q & A(0)
- WAPT Interview Q & A(0)
- VAPT Interview Q & A(50)
- Ethical Hacking Interview Q & A(78)
- Study Material(7)
- IT Exams(53)
- Red Hat Certification(15)
- AWS Certification(1)
- Cyber Security Certification(5)
Random Posts
Tags
- CompTIA PenTest+
- DevOps certifications
- spotting phishing
- AI-generated exploits
- Pentesting with Kali Linux
- Generative AI career guide
- Social Security identity verification
- AI in security automation.
- OpenShift tips
- Code Optimization
- career support
- AI for automated reconnaissance
- Cybersecurity Leadership Roles
- Hydra installation guide
- linux vs windows




![Top 10 Ethical Hackers in the World [2025]](https://www.webasha.com/blog/uploads/images/202408/image_100x75_66c2f983c207b.webp)

![[2025] Top 100+ VAPT Interview Questions and Answers](https://www.webasha.com/blog/uploads/images/image_100x75_6512b1e4b64f7.jpg)









